Understanding Allowlisting: Enhancing Security and Access Control
Allowlisting is a vital cybersecurity practice that controls what is permitted to run or access [...]
Jan
Understanding Employment Scams
Employment scams are increasingly common in today’s digital world, targeting job seekers through deceptive job [...]
Jan
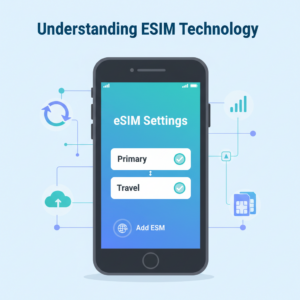
Understanding eSIM Technology
eSIM technology is transforming the way we connect our devices to mobile networks. Unlike traditional [...]
Jan
Understanding Angler Phishing
Angler phishing is a sophisticated type of cyberattack that targets unsuspecting users on social media [...]
Jan
The Birth of the Internet: Understanding ARPANET
The ARPANET marks a revolutionary chapter in technological history, laying the groundwork for what would [...]
Jan
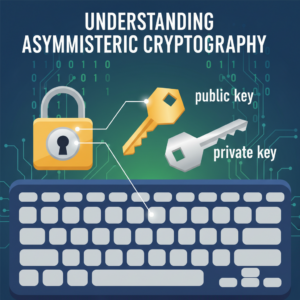
Understanding Asymmetric Cryptography
Asymmetric cryptography stands at the core of secure digital communication, safeguarding sensitive data in countless [...]
Jan
Understanding Augmented Intelligence
Augmented intelligence is reshaping how we work and make decisions by combining the strengths of [...]
Jan
Understanding Bait and Switch
Bait and switch is a deceptive practice that can leave consumers feeling frustrated and misled. [...]
Jan
Understanding Bandwidth Throttling
Bandwidth throttling is a common yet often misunderstood practice in the world of internet connectivity. [...]
Jan


 Русский
Русский Bahasa Indonesia
Bahasa Indonesia فارسی
فارسی