Understanding Bcrypt
Bcrypt is a widely-used password hashing algorithm designed to safeguard sensitive data. As cyber threats [...]
Jan
Understanding Business Email Compromise (BEC)
Business Email Compromise (BEC) is a sophisticated form of cybercrime that targets organizations by exploiting [...]
Jan
Understanding Hotspots and Their Role in Connectivity
In a world where constant connectivity is essential, hotspots have become an everyday tool for [...]
Jan
Understanding Phishing Emails
Phishing emails are a major threat to online security, deceiving recipients into revealing sensitive information [...]
Jan
Understanding the POODLE Attack in Cybersecurity
The POODLE attack is a significant vulnerability in internet security, particularly impacting encrypted communications. Originally [...]
Jan
Understanding Port Out Scams and How to Stay Protected
Port out scams are a growing threat in today’s digital age. This article reveals how [...]
Jan
Understanding Rootkits and Their Impact on Cybersecurity
Rootkits are among the most stealthy and dangerous forms of malware, capable of giving cybercriminals [...]
Jan
Understanding Routers
A router is at the heart of almost every modern network, ensuring our devices connect [...]
Jan
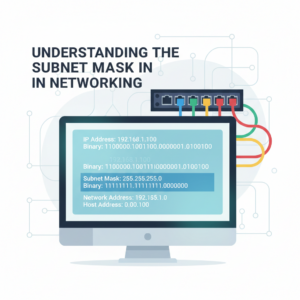
Understanding the Subnet Mask in Networking
A subnet mask is a fundamental concept in computer networking that plays a critical role [...]
Jan


 Русский
Русский Bahasa Indonesia
Bahasa Indonesia فارسی
فارسی